Filter results
Category
- (-) Computing & Analytics (14)
- (-) Atmospheric Science (4)
- (-) Coastal Science (4)
- (-) Energy Storage (2)
- (-) High-Performance Computing (1)
- Scientific Discovery (308)
- Biology (199)
- Earth System Science (136)
- Human Health (103)
- Integrative Omics (74)
- Microbiome Science (42)
- Computational Research (24)
- National Security (21)
- Chemistry (10)
- Energy Resiliency (10)
- Data Analytics & Machine Learning (9)
- Materials Science (7)
- Computational Mathematics & Statistics (6)
- Visual Analytics (6)
- Chemical & Biological Signatures Science (5)
- Renewable Energy (5)
- Weapons of Mass Effect (5)
- Ecosystem Science (4)
- Data Analytics & Machine Learning (3)
- Plant Science (3)
- Cybersecurity (2)
- Distribution (2)
- Electric Grid Modernization (2)
- Energy Efficiency (2)
- Grid Cybersecurity (2)
- Solar Energy (2)
- Bioenergy Technologies (1)
- Computational Mathematics & Statistics (1)
- Grid Analytics (1)
- Subsurface Science (1)
- Terrestrial Aquatics (1)
- Transportation (1)
- Wind Energy (1)
Content type
Tags
- Synthetic (5)
- Energy Equity (2)
- Energy Storage (2)
- Data inventory (1)
- Droughts (1)
- Energy Burden (1)
- Energy Justice (1)
- Extreme weather (1)
- Fires (1)
- Heatwaves (1)
- High-Performance Computing (1)
- Machine Learning (1)
- ML/AI (1)
- Predictive Modeling (1)
- Renewable Energy (1)
- Solar photovoltaics (1)
- Weatherization (1)
HDF5 file containing 10,000 hydraulic transmissivity inputs and the corresponding hydraulic pressure field outputs for a two-dimensional saturated flow model of the Hanford Site. The inputs are generated by sampling a 1,000-dimensional Kosambi-Karhunen-Loève (KKL) model of the transmissivity field...
This data is a model of synthetic adversarial activity surrounded by noise and was funded by DARPA. The various versions include gradually more complex networks of activities.
Category
Datasets
1
Category
Datasets
1
Category
Datasets
1
This data is a model of synthetic adversarial activity surrounded by noise and was funded by DARPA. The various versions include gradually more complex networks of activities.
Category
Datasets
1
Category
Datasets
7
PNNL’s Vision Statement for Equity in the Power Grid Drawing from a wealth of interdisciplinary research in grid modernization, PNNL is spearheading an effort to advance equity and energy justice through the role of scientific research with the goal of building an advanced national power grid...
Datasets
2
This data was generated by the organization IvySys. Activities can be phone calls, transactions, or any other type of communications. Most of the files are of the type .edges, .rdf, or .csv; but all can be opened in a text editor. A good introduction to this data can be found in \Tutorial1\MAA...
Category
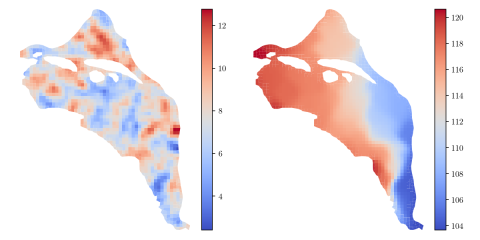
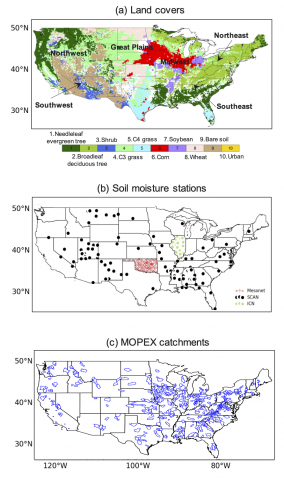
Comprehensive assessment of climate datasets created by statistical or dynamical models is important for effectively communicating model projection and associated uncertainty to stakeholders and decision-makers. The Department of Energy FACETS project aims to foster such communication through...
Category
Category
Dataset The dataset will consist of: About 1200 news stories from the Alderwood Daily News plus a few other items collected by the previous investigators A few photos A few maps of Alderwood and vicinity (in bitmap image form) A few files with other mixed materials, e.g. a spreadsheet with voter...
Category
It is Fall of 2004 and one of your analyst colleagues has been called away from her current tasks to an emergency. The boss has given you the assignment of picking up her investigation and completing her task. She has been asked to pursue a line of investigation into some unexpected activities...
Category
Mini Challenge 1: Wiki Editors The Paraiso movement is controversial and is having considerable social impact in a specific area of the world. We have extracted a segment of the Paraiso (the movement) Wikipedia edits page. Please note this is not the Paraiso Manifesto Wiki page which is part of the...
Category
The VAST 2009 Challenge scenario concerned a fictitious, cyber security event. An employee leaked important information from an embassy to a criminal organization. Participants were asked to discover the identity ofthe employee and the structure of the criminal organization. Participants were...