The VAST 2009 Challenge scenario concerned a fictitious, cyber security event. An employee leaked important information from an embassy to a criminal organization. Participants were asked to discover the identity ofthe employee and the structure of the criminal organization. Participants were...
Filter results
Category
- (-) National Security (21)
- Scientific Discovery (307)
- Biology (198)
- Earth System Science (136)
- Human Health (102)
- Integrative Omics (73)
- Microbiome Science (42)
- Computational Research (23)
- Computing & Analytics (14)
- Chemistry (10)
- Energy Resiliency (9)
- Data Analytics & Machine Learning (8)
- Materials Science (7)
- Visual Analytics (6)
- Chemical & Biological Signatures Science (5)
- Computational Mathematics & Statistics (5)
- Weapons of Mass Effect (5)
- Atmospheric Science (4)
- Coastal Science (4)
- Ecosystem Science (4)
- Renewable Energy (4)
- Data Analytics & Machine Learning (3)
- Plant Science (3)
- Cybersecurity (2)
- Distribution (2)
- Electric Grid Modernization (2)
- Energy Efficiency (2)
- Energy Storage (2)
- Grid Cybersecurity (2)
- Solar Energy (2)
- Bioenergy Technologies (1)
- Computational Mathematics & Statistics (1)
- Grid Analytics (1)
- High-Performance Computing (1)
- Subsurface Science (1)
- Terrestrial Aquatics (1)
- Transportation (1)
- Wind Energy (1)
Content type
Tags
- Synthetic (5)
- Cybersecurity (2)
- Electrical energy (2)
- Proteomics (2)
- Data inventory (1)
- Droughts (1)
- EBC (1)
- Exhaled Breath Condensate (1)
- Extreme weather (1)
- Fires (1)
- Heatwaves (1)
- High-Performance Computing (1)
- Machine Learning (1)
- ML/AI (1)
- Omics (1)
- Predictive Modeling (1)
- Quantification (1)
- TMT (1)
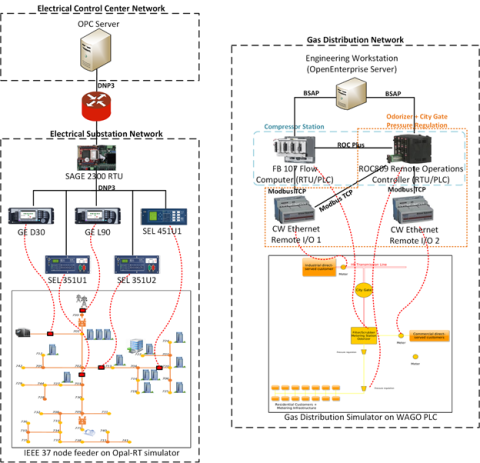
This dataset includes the results of high-fidelity, hardware in the loop experimentation on simulated models of representative electric and natural gas distribution systems with real cyber attack test cases. Such datasets are extremely important not only in understanding the system behavior during...
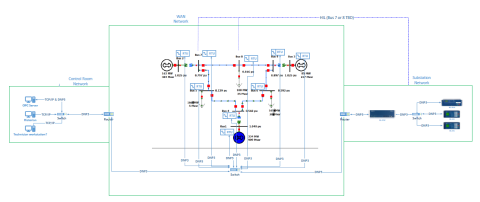
This dataset includes one baseline and three cybersecurity based scenarios utilizing the IEEE 9 Bus Model. This instantiation of the IEEE 9 model was built utilizing the OpalRT Simulator ePhasorsim module, with Bus 7 represented by hardware in the loop (HiL). The HiL was represented by two SEL351s...
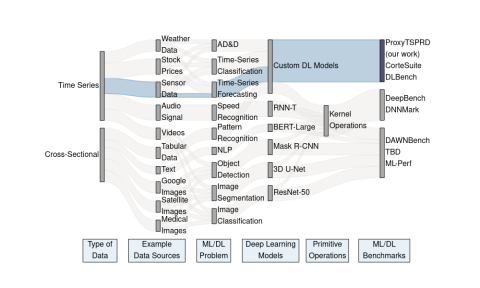
ProxyTSPRD profiles are collected using NVIDIA Nsight Systems version 2020.3.2.6-87e152c and capture computational patterns from training deep learning-based time-series proxy-applications on four different levels: models (Long short-term Memory and Convolutional Neural Network), DL frameworks...
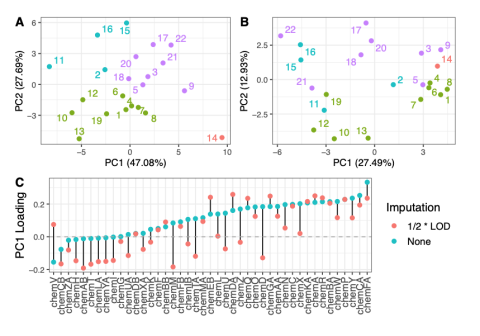
This data is supplementary to the manuscript Expanding the access of wearable silicone wristbands in community-engaged research through best practices in data analysis and integration by Lisa M. Bramer, Holly M. Dixon, David J. Degnan, Diana Rohlman, Julie B. Herbstman, Kim A. Anderson, and Katrina...
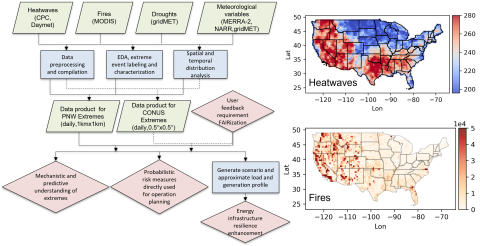
Extreme weather events, including fires, heatwaves(HWs), and droughts, have significant impacts on earth, environmental, and power energy systems. Mechanistic and predictive understanding, as well as probabilistic risk assessment of these extreme weather events, are crucial for detecting, planning...