Last updated on 2024-02-11T22:41:43+00:00 by LN Anderson West Nile Virus Experiment WGCN002 The purpose of this experiment was to evaluate the host response to West Nile virus (strain WNV-NY99) wild-type clone 382 and mutant 382-E218A virus infection. Sample data was obtained from mouse (strain...
Filter results
Content type
Tags
- (-) Mus musculus (15)
- Virology (63)
- Immune Response (48)
- Time Sampled Measurement Datasets (45)
- Gene expression profile data (42)
- Differential Expression Analysis (41)
- Homo sapiens (30)
- Mass spectrometry data (25)
- Multi-Omics (23)
- MERS-CoV (16)
- Viruses (14)
- Health (13)
- Soil Microbiology (13)
- Virus (13)
- West Nile virus (11)
- Synthetic (10)
- Ebola (9)
- Influenza A (9)
- sequencing (9)
- Resource Metadata (8)
- Metagenomics (7)
- Microarray (5)
- Genomics (4)
- Human Interferon (4)
- Microbiome (4)
- Omics (4)
- IAREC (3)
- metagenomics (3)
- Sequencing (3)
- soil microbiology (3)
Last updated on 2024-02-11T22:41:43+00:00 by LN Anderson West Nile Virus Experiment WGCN003 The purpose of this experiment was to evaluate the host response to West Nile virus (strain WNV-NY99) wild-type clone 382 and mutant 382-E218A virus infection. Sample data was obtained from mouse (strain...
Category
Last updated on 2024-02-11T22:41:43+00:00 by LN Anderson West Nile Virus Experiment WCN003 The purpose of this experiment was to evaluate the host response to West Nile virus (strain WNV-NY99) wild-type clone 382 and mutant 382-E218A virus infection. Sample data was obtained from mouse (strain C57BL...
Category
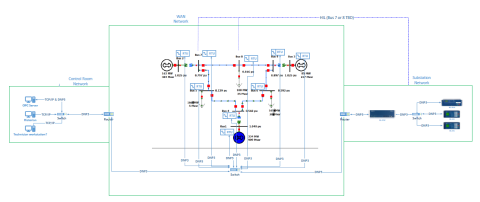
This dataset includes one baseline and three cybersecurity based scenarios utilizing the IEEE 9 Bus Model. This instantiation of the IEEE 9 model was built utilizing the OpalRT Simulator ePhasorsim module, with Bus 7 represented by hardware in the loop (HiL). The HiL was represented by two SEL351s...
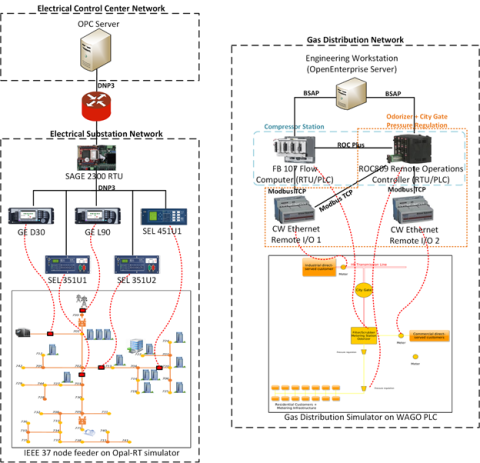
This dataset includes the results of high-fidelity, hardware in the loop experimentation on simulated models of representative electric and natural gas distribution systems with real cyber attack test cases. Such datasets are extremely important not only in understanding the system behavior during...